Purpose of the Promiscuous Mode Scanner tool
The Promiscuous Mode Scanner Tool scans your subnet for network interfaces listening for all ethernet packets in Promiscuous Mode.About the Promiscuous Mode Scanner Tool
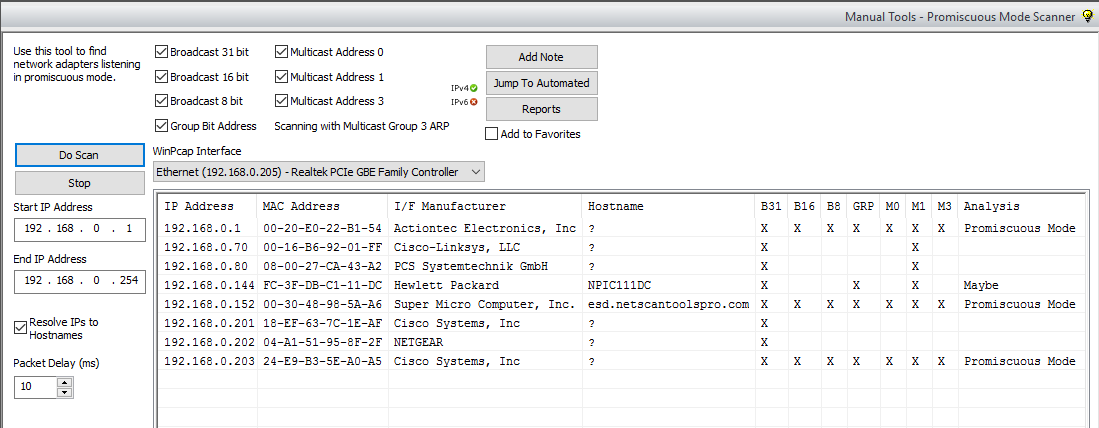
The Promiscuous Mode Scanner Tool scans your subnet and shows network interfaces listening in Promiscuous Mode. Interfaces operating in that mode are listening for all packets, not just packets destined for that specific interface.
Related Tool Links
How the Promiscuous Mode Scanner Tool works
This tool actively scans your subnet with modified ARP packets and shows the devices responding to each type of ARP packets.
The devices that respond to nearly every packet are most likely listening in Promiscuous Mode (ie. the ethernet interface is capturing IP packets not intended for that IP address). All IPv4 devices MUST respond to ARP even if they are running a firewall and invisible to normal ICMP Ping. Note that ARP is not routed so you are limited to your subnet.
The image below shows a DSL router in the first row listening in Promiscuous Mode which would be expected from this type of device.
Note that the scanner requires the use of WinPcap. We install WinPcap as part of the installation package. WinPcap is designed for wired ethernet cards, not cellular modems and it usually works well with 802.11x wireless interfaces.
A video of the Promiscuous Mode Scanner Tool in action!
Link to YouTube Video (If you click on the link below, you will be leaving our website - Warning - YouTube uses cookies)Promiscuous Mode Scanner demonstration video
Try the NetScanTools Pro demo free for 14 days
DEMO Version End User License Agreement (EULA)How to Uninstall