Purpose of the SNMP - Core
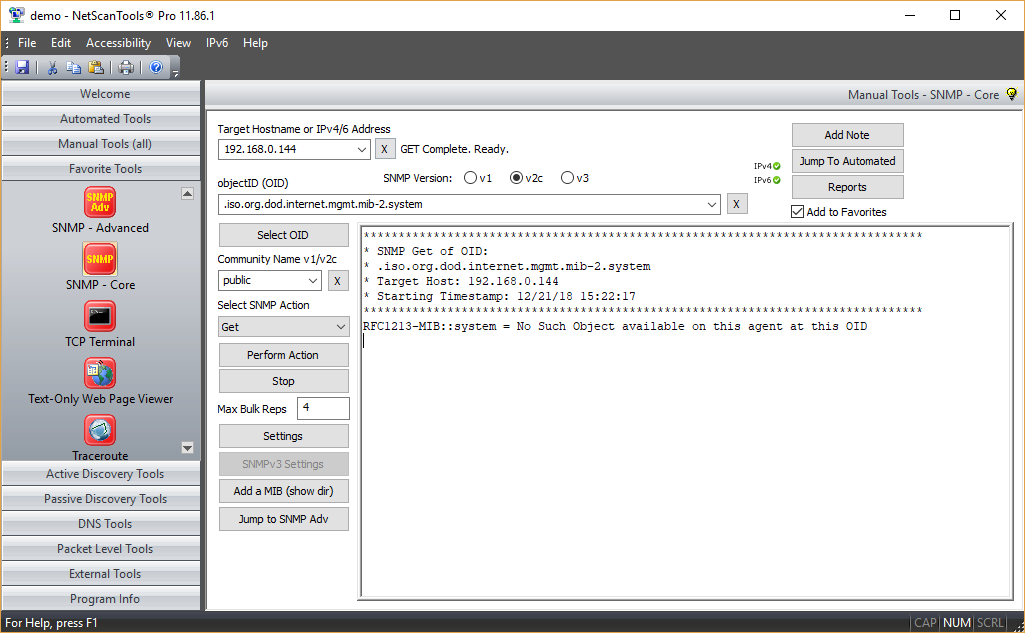
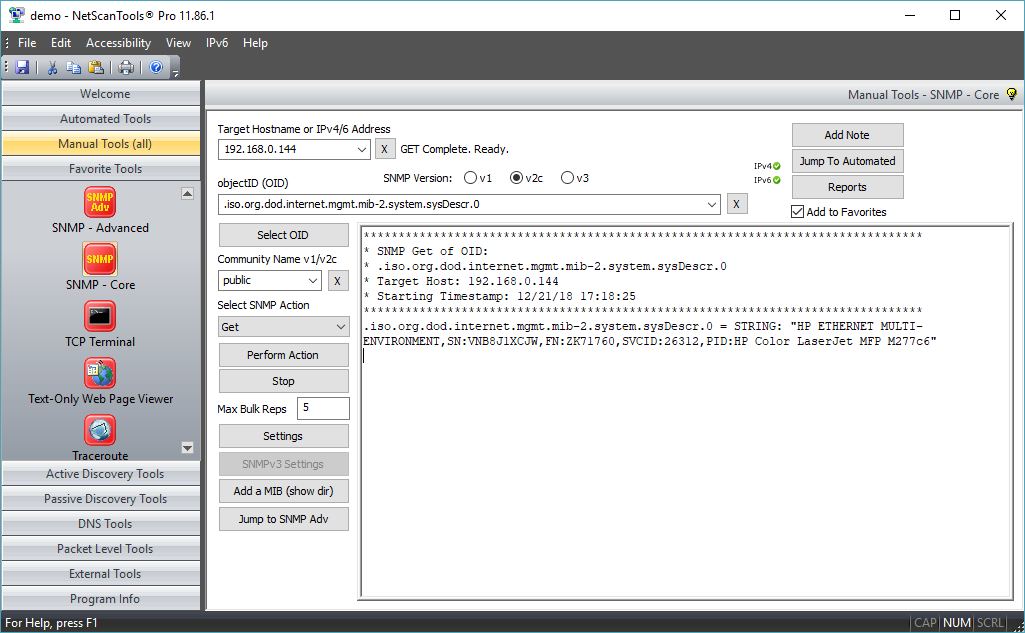
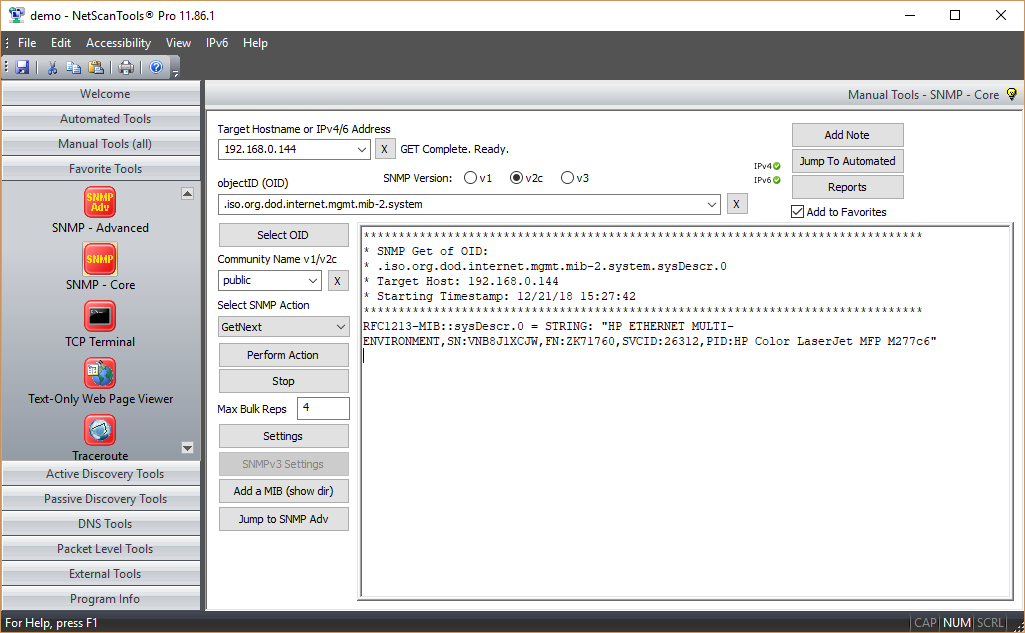
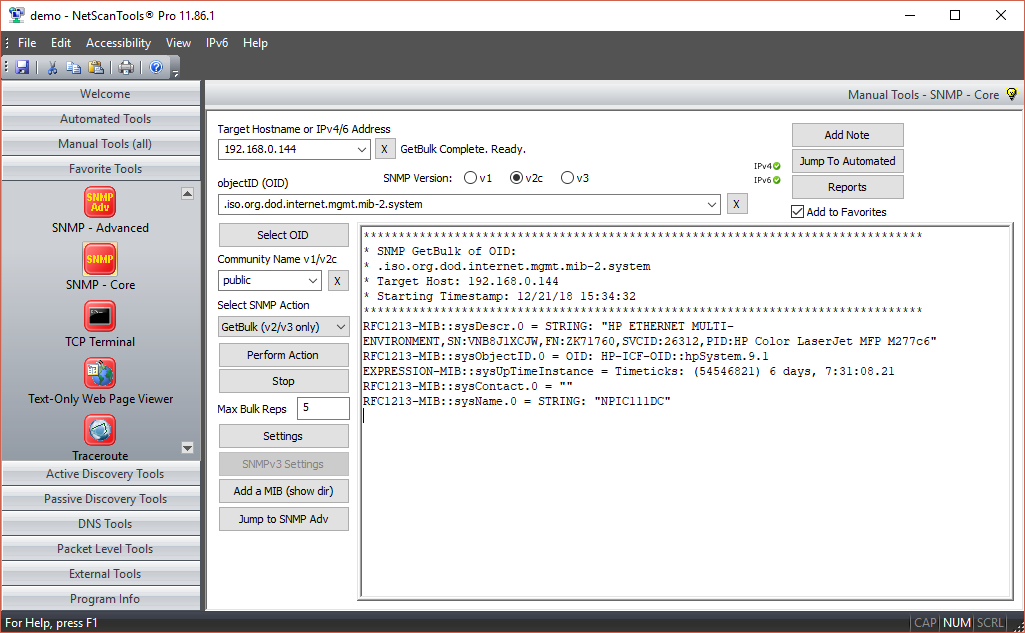
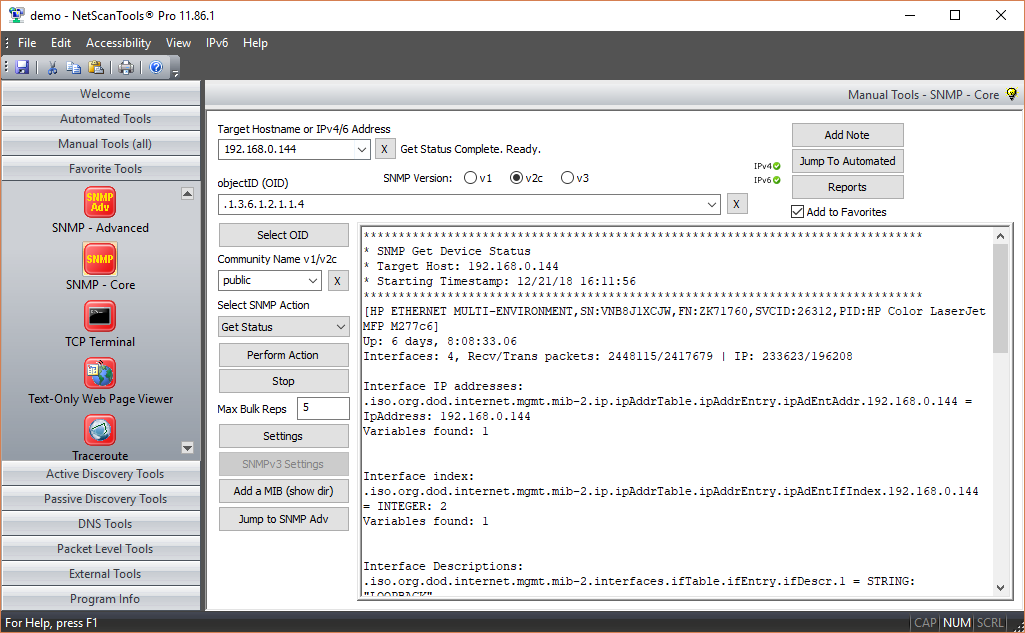
The purpose of this tool is to create SNMP queries to send to a target, listen for and display the response from the target. If the target is running SNMP and you have the proper access credentials, you can gain an enormous amount of information about the target.About SNMP - Core
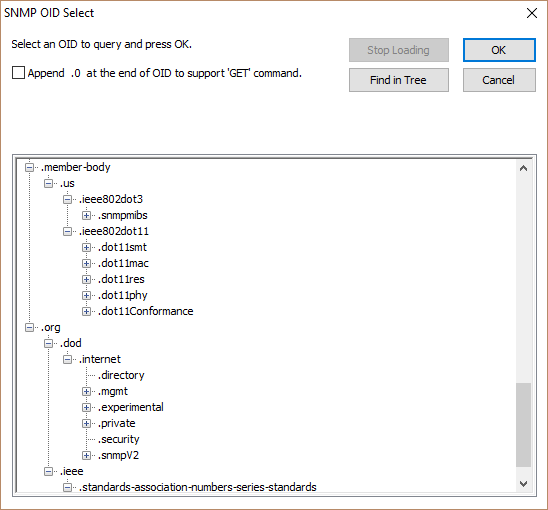
SNMP (Simple Network Management Protocol) is one of the most powerful tools in NetScanTools Pro. The purpose of this tool is to provide a way to communicate with SNMP enabled devices using SNMP version 1, 2c and version 3. You can gather a wealth of detailed information about the target system provided the target is running SNMP and you have the right access credentials (community name or SNMPv3 access). Devices that run SNMP include network switches, routers and even Windows computers. Supports both IPv4 and IPv6 communication with targets.Here are examples of data you can obtain:
- Detailed information about the type of system, model number, including operating system type, revision, system uptime, serial number, and sometimes information like the names of the contact person and the computer location.
- Listening process/daemon programs running on the target.
- Network Interface details such as the IPv4/IPv6 address(es) and MAC address, speed, MTU and status of each interface.
- TCP, UDP, ICMP, IP protocol real time statistics.
- All kinds of statistics about packets, device status, etc.
- Bridging data showing MAC addresses of devices attached to bridge ports.
- The LAN manager data.
- Virtually anything the device is allowed to provide given the permissions of the access credentials you are using.
A core set of SNMP Tools
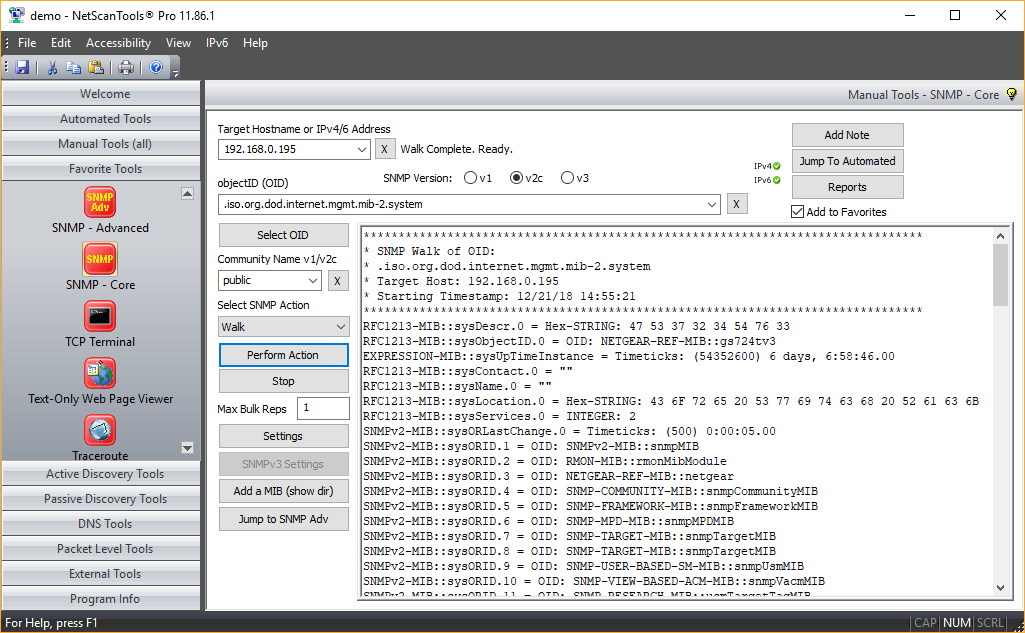
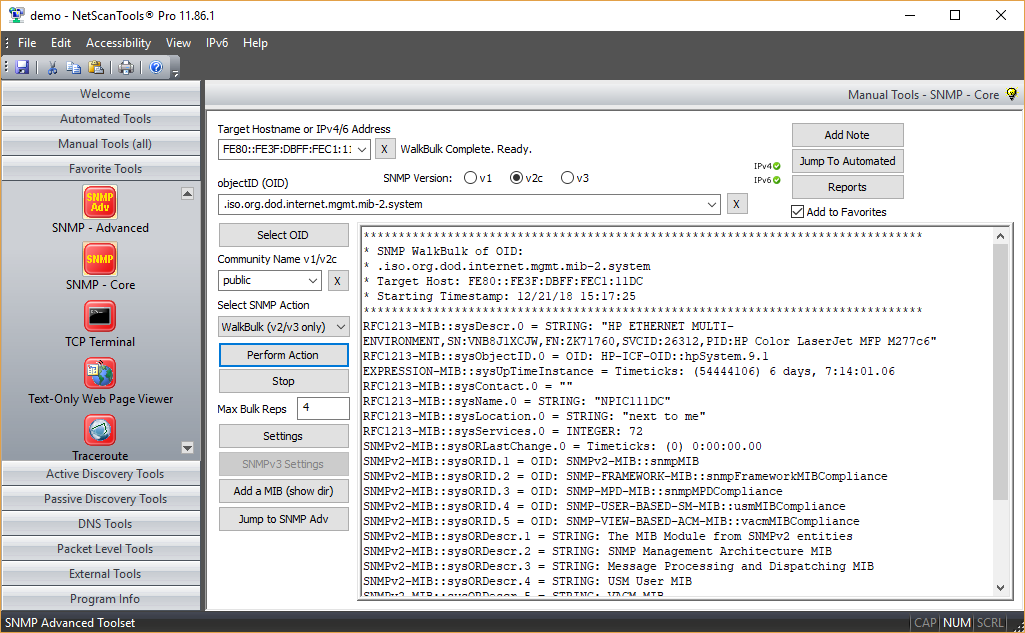
Selecting a MIB from the loaded MIB set
[Select OID...] button. Used to bring up a selection tree for choosing the OID (object identifier) number to use during your queries. OIDs are like database indexes to a particular object of data which may be static or dynamically updated in real time. This selection tree is built using the currently loaded OIDs. Includes a Find in Tree button to search for labels in the tree.
Walk (SNMPv1, v2c and v3)
OID numbers are organized in a directory tree structure, the walk command will allow you to view all the subitem entries and their data values for a particular parent OID. In 'walk', every data response is due to a request - Max Bulk Reps is ignored.
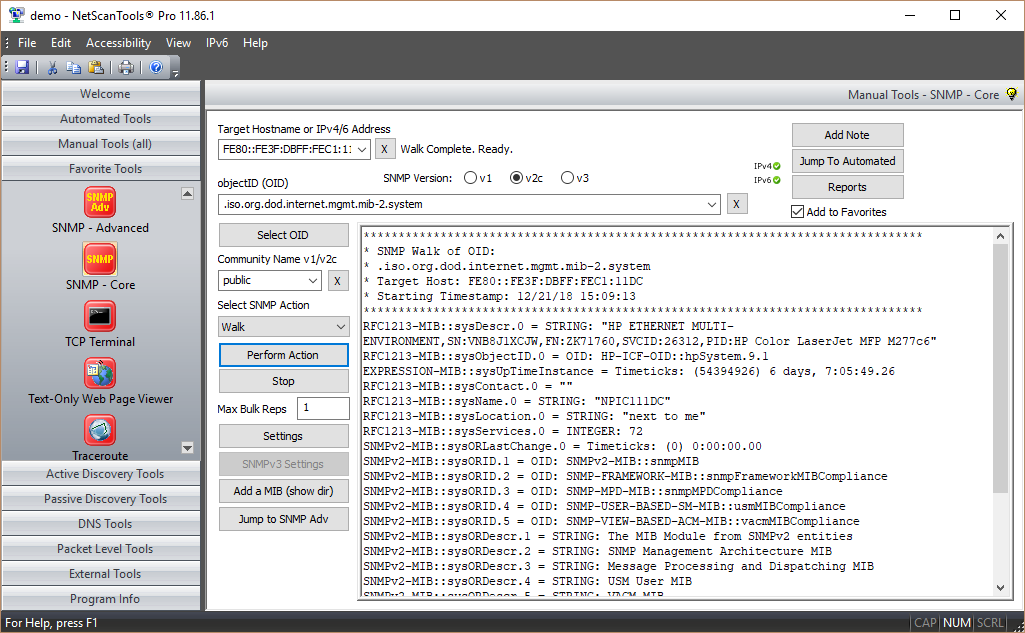
WalkBulk (v2c and v3)
OID numbers are organized in a directory tree structure, the WalkBulk command will allow you to view all the subitem entries and their data values for a particular parent OID. In 'WalkBulk', multiple data responses are due to a single request with the maximum responses a function of Max Bulk Reps, usually set at 8 or lower. There is no difference in the data compared with Walk, only in the method and efficiency of data transfer.
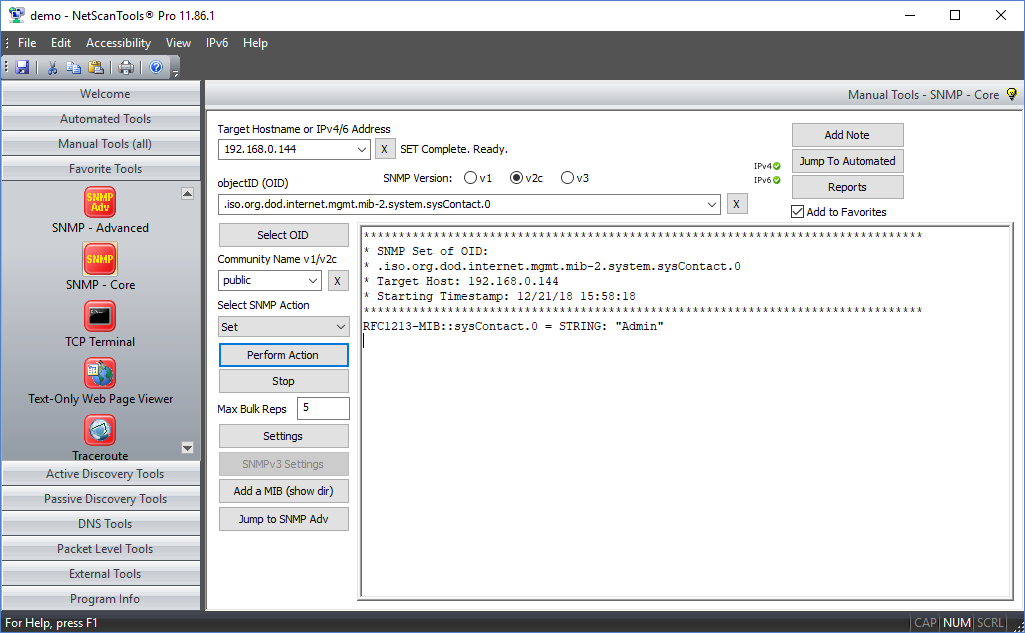
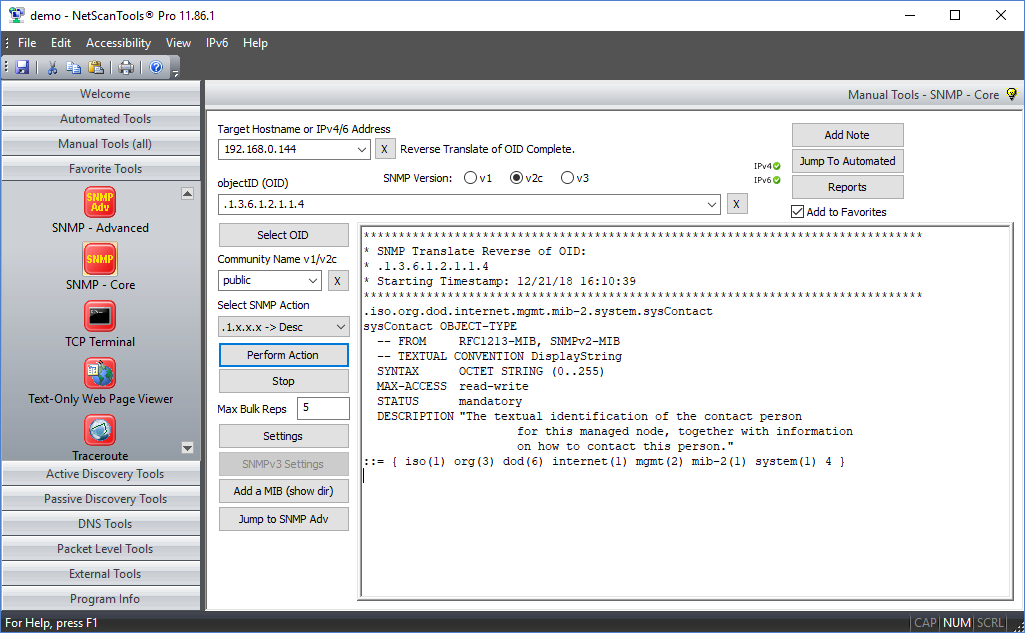
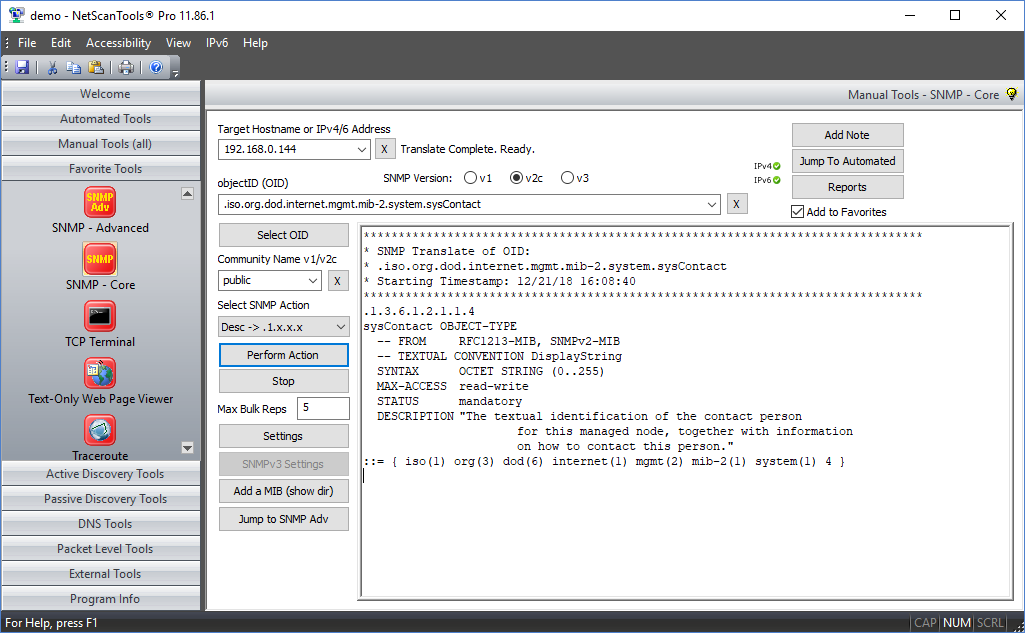
Translate and get Description of OID
This option allows you to translate a numeric OID to fully qualified MIB representation along with the description or go the other way and enter the fully qualified MIB representation to see the numeric OID with description.
A video of SNMP - Core in action!
Not yet available.Try the NetScanTools Pro demo free for 14 days
DEMO Version End User License Agreement (EULA)How to Uninstall